Sandfly 2.4.0 – Splunk Support, Reconnaissance, Process Injection Detection and Containers
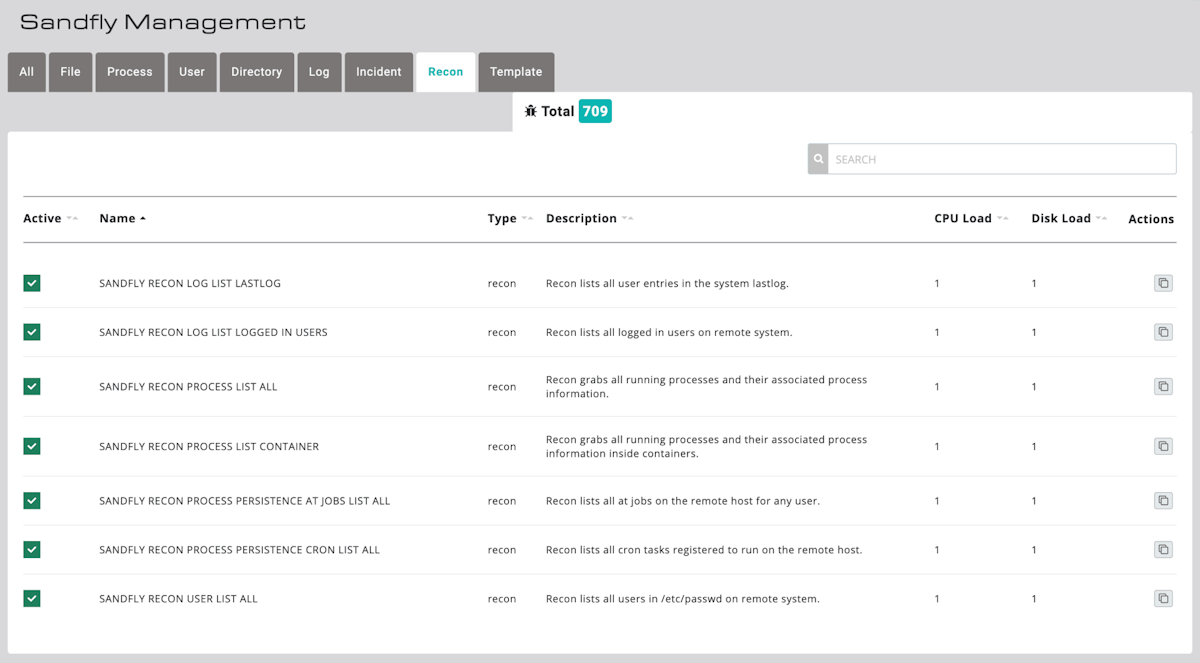
Sandfly 2.4.0 has been released with major new features. We have boosted our Linux intrusion detection and incident response signatures to over 700. We have also begun building out the ability to detect advanced process injection attacks and expanded our container compromise support. Finally, we have enabled new features to support our upcoming Splunk app. Let’s go over all of these changes because there are a lot of them.
Reconnaissance Sandflies
The first major change is we have introduced a new type of reconnaissance (recon) Sandfly. Prior versions had intrusion detection sandflies that looked for file, process, directory, user and log attacks. Additional sandflies were also included for incident response and templates for custom applications. Now, we have a new recon Sandfly type.
Recon sandflies gather remote system information with our agentless forensic engines that can be used to build machine learning detection models and help with threat hunting. Our first application to support this feature will be available for Splunk which will be announced shortly.
Recon sandflies gather information such as running processes, logged in users, past logins, cron jobs, and other forensic data. This data can then be queried and aggregated by analytics engines and used to detect subtle and not-so-subtle attacks. Not just this, but it can also be used to build a past record of what was running on the system, who was logged in, what user accounts existed, etc. and this can be queried like any other record. This is perfect for threat hunting, compliance and incident response.
Customers using a Security Information Event Manager (SIEM) like Splunk will be able to apply advanced analytics to a rich dataset from Linux not available before. And of course, it all happens without loading any agents on your endpoints.
Splunk App Coming
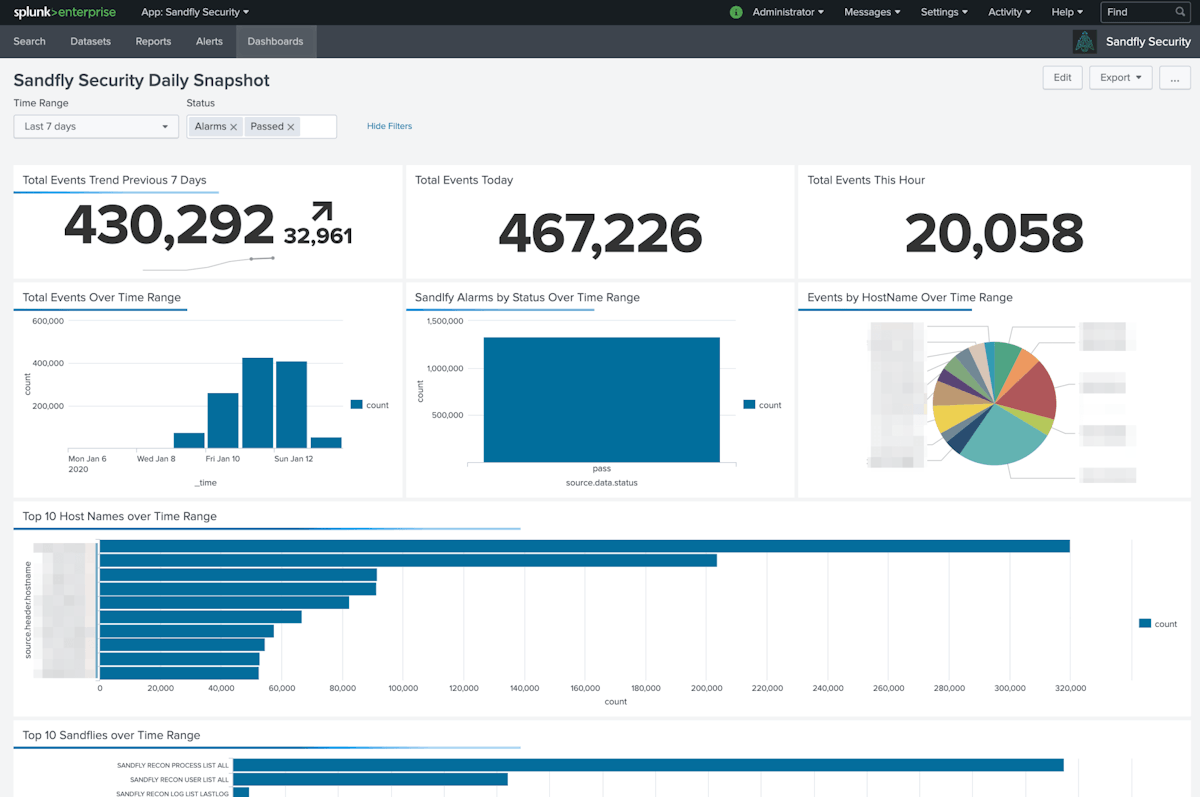
Splunk is the industry-leading SIEM and data analytics tool. As Splunk users know, it’s powerful and able to process data to produce extensive reports and assist threat hunting. However, Splunk (like all these tools) can only analyze the data they receive. As it turns out, getting consistently rich and valuable data from Linux is very hard. Often admins need to resort to audit logs that lack details and have inconsistent formatting that makes analysis difficult. Or, they need to load agents everywhere which is risky and often not practical.
Sandfly is here to fix these problems. Our agentless approach means Splunk users will now have instant visibility to all their Linux hosts with data that is designed specifically for security and forensics. If you have SSH access to your Linux endpoints, then Sandfly can run on them today and get this data.
Linux Visibility Without Agents
One of the biggest problems with Linux is that it’s very hard to get visibility across all the platforms and distributions. Many organizations run CentOS, RedHat, Ubuntu, Debian, Fedora, Amazon Linux, Suse or all of them (at once). Organizations run Linux across physical hardware, Virtual Machines, cloud providers and even embedded devices like Raspberry Pi. Running agents all over the place is impractical in these real-world scenarios. Even if you could do it, agents often lack details that are
Sandfly solves these problems. We have extensive visibility across Linux for almost every CPU type from Intel to AMD to Arm to MIPS. If it runs Linux, chances are Sandfly can work on it and provide security visibility instantly without remote system impacts.
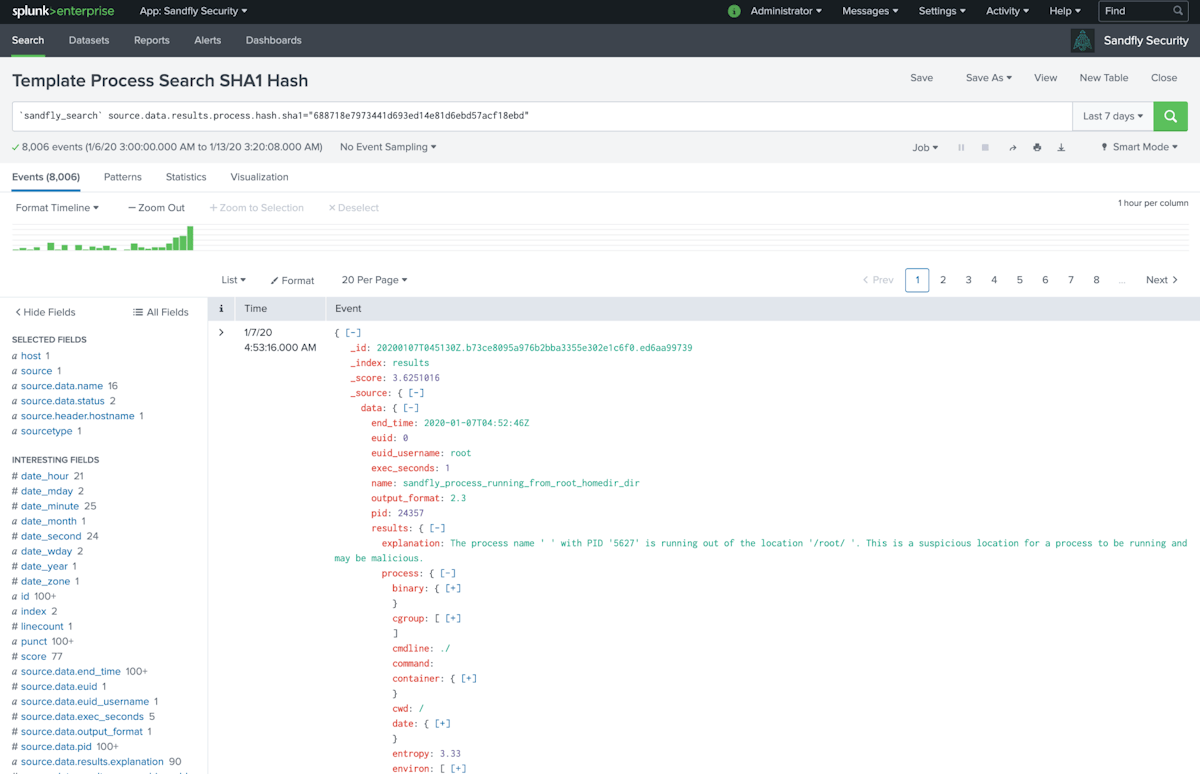
What can you do with this visibility? Here are some search ideas:
Process names that are running or have run on your Linux hosts going back as far as you have saved the data.
Process hashes to see if a known malicious or suspicious binary has ever run on your hosts or is running right now.
Usernames that are logged in or have ever logged in and where they originated.
Usernames that have passwords enabled, SSH keys present or are running obsolete password hashes.
Past or present network ports operating and what they were connected to at the time.
Operating System values such as kernel versions, memory available, distribution names, mounts, CPU bugs and more.
The list of possibilities here is very large. If you are running Linux and don’t have visibility to do the above today, you will now have it with Sandfly and Splunk.
Process Injection Attacks and More
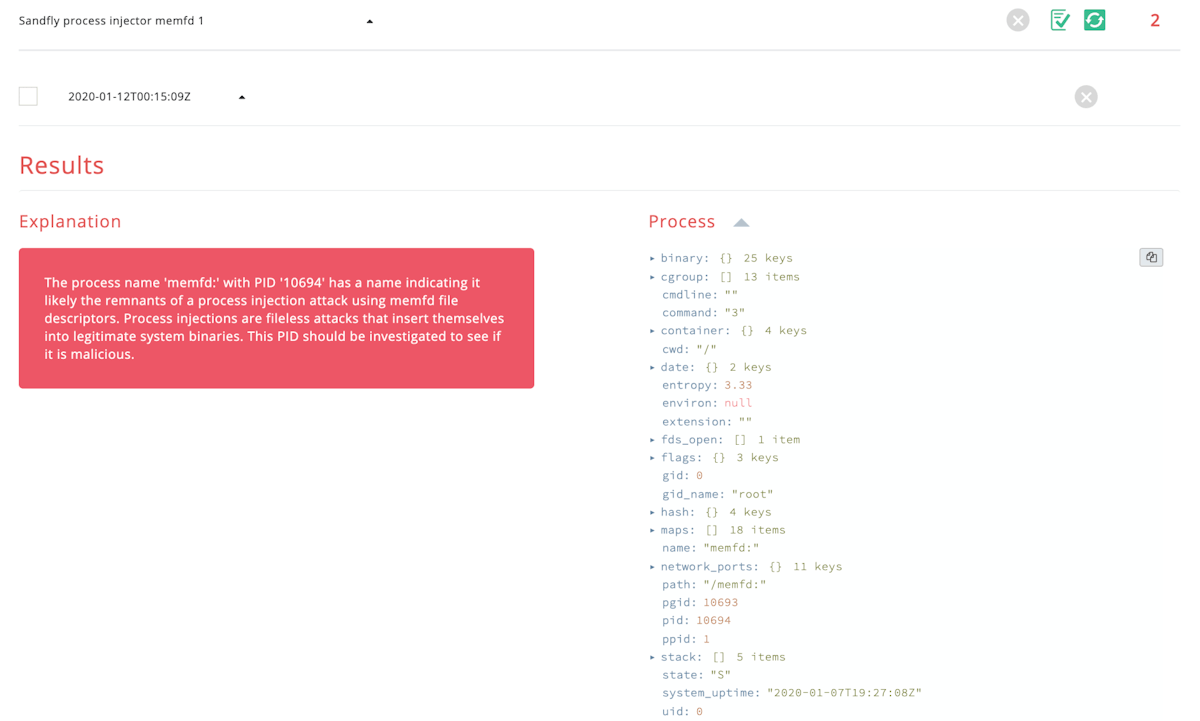
We have added in Sandfly checks to detect process injection attacks for Linux and will be expanding this capability as we move forward. This is an advanced technique, but is getting more attention today and we have coverage for it in multiple ways.
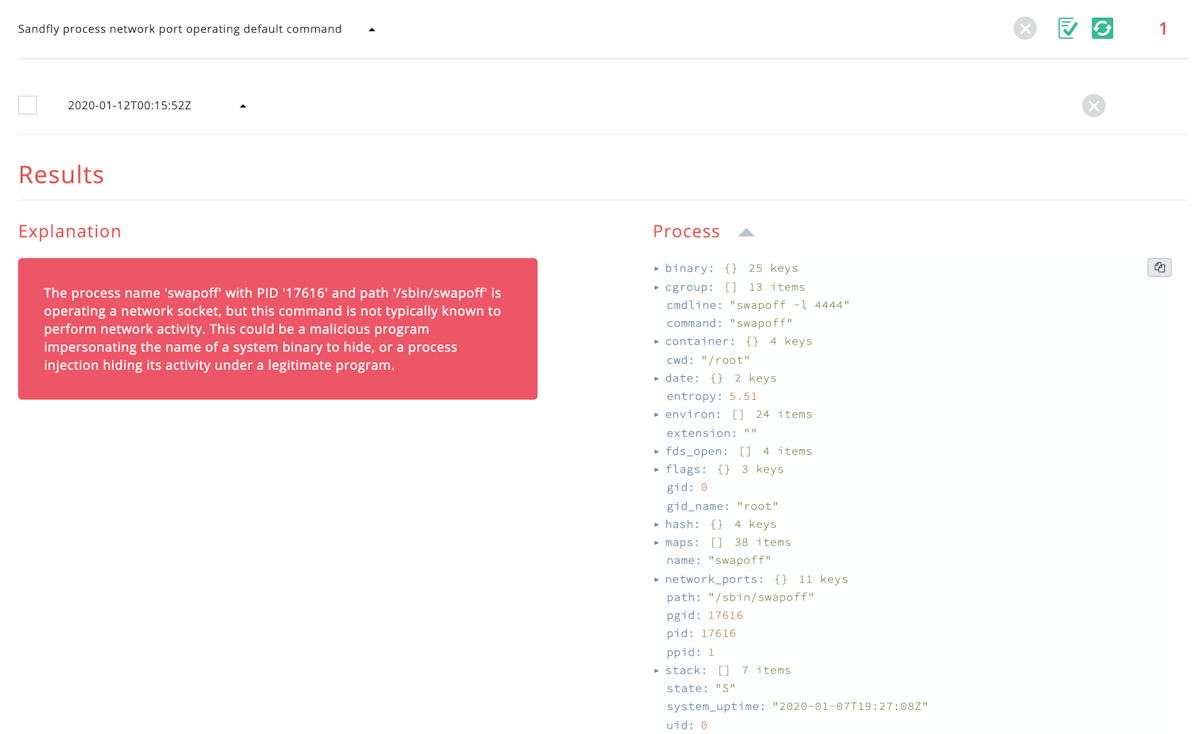
We have also added in Sandfly checks to look for default system commands using network ports where normally we wouldn’t expect to see them. This is a masquerading tactic where a system binary is replaced or attacked to make it listen on a network port or do other malicious activity.
In addition to the above we have made the following new or improved Sandfly checks:
New checks for processes connecting to suspicious paste sites known to harbor malware and malicious scripts.
Multiple process injection detection methods.
Hidden or suspiciously named LD_PRELOAD paths often linked to stealth rootkit activity.
Log file tampering detection now supports Arm and MIPS CPUs along with previous Intel/AMD variants.
Immutable files under system cron directories are now flagged as malicious.
Improved detection of netcat, socat and other backdoors inside system init and update scripts.
Cron backdoor detection improved and expanded.
At job backdoor detection improved and expanded.
Login/logout persistence attacks improved and expanded.
Network initialization scripts now checked for backdoors and suspicious commands.
OS identification of hosts now includes all mounted file systems.
Docker Container Compromise Detection
Sandfly has always been able to agentlessly detect suspicious and compromised processes inside Docker containers since version 1.0. We are now formalizing this capability by building out new features specific to container compromise detection. We are able to do container inspection completely agentlessly as we do today, but we are going to be adding some unique twists in upcoming releases.
Bug Fixes
We have various bug fixes in this update as well:
Sandflies will retain their active/inactive state during upgrades.
Fixed self-signed certificate errors generated in Chrome 75 and above.
utmp/wtmp/btmp log file tampering detection on Arm/MIPS fixed.
UI upgrades and fixes.
How to Upgrade Sandfly
Sandfly is easy to upgrade. Please follow the instructions here:
Over 700 Sandfly Checks and Growing
Sandfly 2.4.0 has now brought the number of compromise and incident response checks we do on Linux up over 700. We can spot a tremendous amount of Linux malware, rootkits and intruder activity without loading any agents on your endpoints and without disruptive updates. Thank you for using our product.